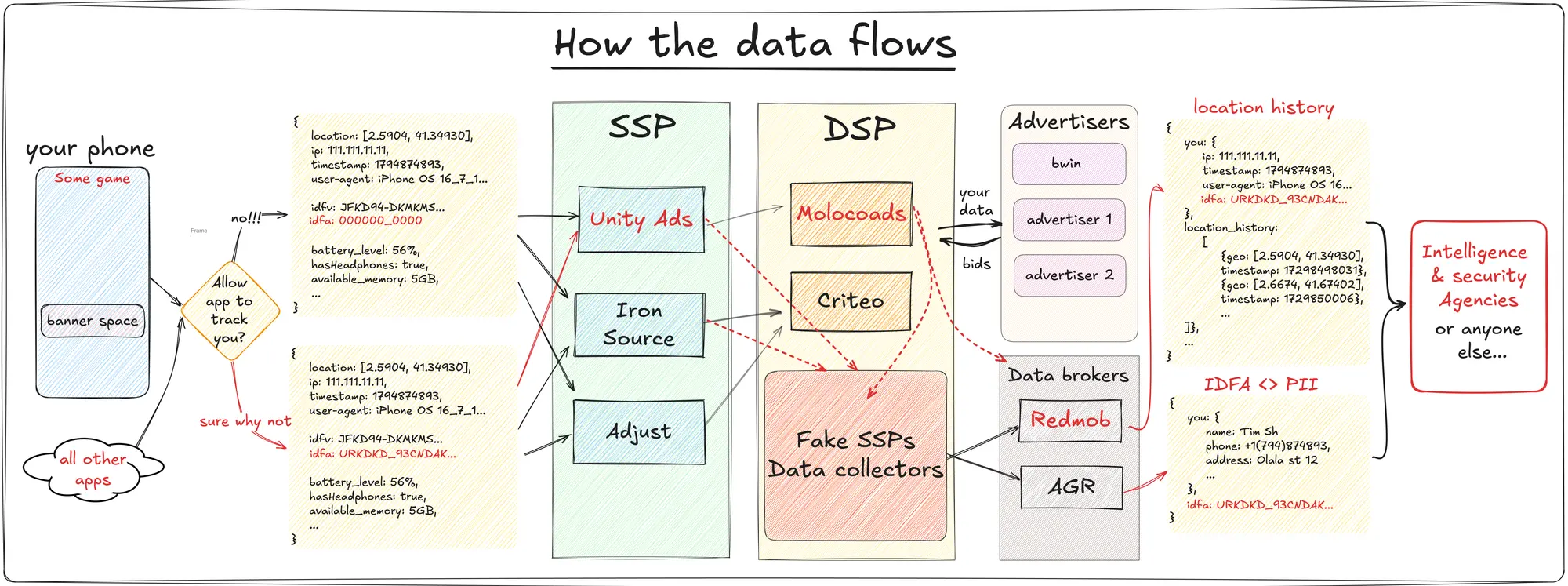
An amazing bit of digital detective work here. Seems like Linux mobile is your only off ramp from being exhaustively tracked
Does this happen to users in the EU? It’s highly illegal to gather data without consent here obviously. Even processing other data to derive location (which is personally identifiable information) means processing data for purpose that’s different to one that was consented to (if they tried to get any consent at all). There are big companies implicated here so it’d be easy to fine them into submission in jurisdictions that allow it.
The sample data shared in the article includes
"c": "ES", // Country code,ES is usually used for Spain, so it looks like these tests were run from within the EU.
Ah, there’s also this piece in json:
"uc": "1", // User consent for tracking = True; OK what ?!My guess is that developers are pretending to get user consent to get more money from the ads. Unity could be encouraging this somehow but good luck proving that.
it’s been known for a long time that there is enough identifiable information in a “normal” person’s internet usage to identify exactly who and where you are and what you are likely doing just from metadata analysis and public domain information
question is, how is this being abused
All HTTP requests include your ip address, you don’t “consent” to giving it to anybody. You can geolocate somebody based on ip address but it won’t be very accurate
True, it’s storing the IP address that is the issue.
Storing it and associating it with all the other identifying information collected.
but it won’t be very accurate
Which they actually acknowledge in the blog post.
Kind of interesting that they’re smart enough to understand how to sniff packets but not enough to understand that IP address = location.
Use a VPN. Problem solved.
Using a VPN just moves the trust to another middleman.
Yeah, a middleman you get to choose. That’s a huge improvement. There are plenty of trustworthy VPN providers.
So use a trustworthy middleman? Surely you can find someone more trustworthy than advertising companies?
You can set up wireguard vpn on a tiny instance in Amazon or Google, and bounce traffic through that one. Then you control what gets logged (Amazon may have logs over all outgoing connections from all instances somewhere though).
You can even make it change it’s public ip every day if you want.
This problem solved, but whenever you change your network or IP and then periodically, your phone will report to Firebase, so you can receive push notifications.
You can block those with software that simulates a local VPN with a filter, but you won’t get any more push notifications. Now push notifications are not just the ones you see. Some apps use invisible ones to get infos they need to work.
Make sure you disable or properly configure webrtc. Even with a VPN it will leak your true IP address.
Check here.
Not the magic bullet people think they are. Oh, and you can’t turn it off, so you’ll have to take the loss in network speed on absolutely everything. And better know how to configure each device so it doesn’t go ahead and check leak your IP anyways, which also restricts choice of devices you use. Cause remember, if any device on your network ever connects to the net without the VPN, then your anonymity just went out the window.
Not the magic bullet people think they are.
No one thinks VPNs are “magic bullets”. I don’t know why this gets repeated ad nauseum.
Oh, and you can’t turn it off, so you’ll have to take the loss in network speed on absolutely everything.
True but it’s not that bad.
And better know how to configure each device so it doesn’t go ahead and check leak your IP anyways
Just choose a good provider. You don’t need to configure anything.
if any device on your network ever connects to the net without the VPN, then your anonymity just went out the window.
That’s what kill switches are for.
I agree it’s a powerful tool! I was specifically responding to “problem solved” in the previous comment. My reply was in no way meant as a general review of VPNs.
That VPN provider will then know ALL the connections you make. Almost worse than just using the Internet normally.
Is there any straightforward way of stopping this besides dropping off the grid?
Using firefox in strict mode with ublock origin, cookie auto-delete, and a VPN to change your IP every now and then should stop location tracking and cross-site tracking. Sites will still know you’ve visited them and what pages you’ve been to in that session, but that is impossible to stop.
The main thing is don’t use apps, they can collect tons of data and tie it directly to your physical device, and run in the background while not actively using it.
Using a web browser is really the safest option I can think of because you have control over almost everything.
I imagine an ad blocker could prevent this data going out, unless the hosts were generic and the game/app simply won’t work without allowing those connections. I’ve never seen an app be [obviously] broken from my ad blocker but I am interested in running a similar experiment to see just how much data is going out.
Route all or traffic through tor. Never log into anything. Never use the same identity twice. Ahh and live in a hut in the woods never going to shops or cities that have security cameras.
I think it’s more: “Don’t use a smartphone”. It’ll send those requests through any internet connection. No matter if it’s a VPN or Tor.
I forgot I’m in a minority of people running a properly secure degoogled ROM.
Same, same. But the occasional app refusing to work due to missing Play services, all the Instagram posts everyone except me took notice of, and all the hoops I have to jump through, kind of remind me of that regularly.
…where are chains allowed to abuse security camera footage for ad tracking?
Bunnings in Australia until very recently and u have basically 0 protections in the states.
Wonder how the app sent geolocation with Location Services disabled.
Even with Linux it wouldn’t be that safe, if apps were doing this crap.
We just have to stop using the internet at this point