Running things from random directories (like ~/Applications which AppimagePool uses) destroys that.
~/Applications is no a random place, it comes from macos. And what is appimagepool?
You mean appimagetool? that’s used to turn the AppDir into an appimage.
If you meant appimagelauncher, ~/Applications is the default location but it can be changed to any location.
(including appimages which are nearly impossible to sandbox)
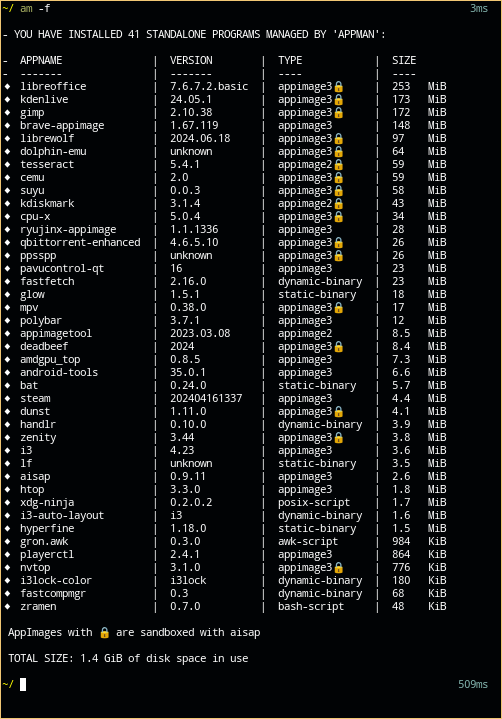
See that lock next to some appimages? Yes that’s aisap sandbox..
It isn’t perfect though, right now its biggest limitation is that a sandboxed appimage can’t launch another sandboxed appimage. But dbus, pipewire, vulkan, themes, etc works.
The “open with” and “create new” things. Actually,
You can totally do that with appimages once they are integrated into the system by the previously mentioned tools, those menus rely on desktop entries in $XDG_DATA_HOME/Applications.
That concept is so broken that it needs to go.
Good thing we have choices on linux, you can make your entire home not executable if you want to.
I like to keep all the software that I need in my home, because that way I don’t depend on what my distro provides. I can just drop my home anywhere (besides a musl distro) and I’m ready to go, I even have my window manager as an appimage because I couldn’t compile it statically.
But the issue is that they were just thrown out there, “here devs, do the same shit you do on Windows, it is totally normal for people to double click an executable, not have any sandboxing, deal with updates on their own, dont have any cryptographic verification, …”.
AppImage is just a format, same as a deb or rpm, you decide how you handle it afterwards.
doing the actual update process (instead of deleting a file and placing a new one)
Same link again: https://github.com/AppImageCommunity/AppImageUpdate
Many of the appimage devs actually worked on making zsync2 for this: https://github.com/AppImageCommunity/zsync2
On Android you still have a package manager but the APKs are signed individually, updates just allowed if the signatures match. So you can sideload how you want, it is still secure.
You mean the APK itself does the signature verification or what? With appimage it is AppImageUpdateTool that does the verification.
(appimages are impossible to sandbox with bubblewrap, and hard with firejail (which is a setuid binary and had security issues), dont know about nsjail, crabjail, minijail or others)
Regarding what?
You still have that github repo saying that appimages bloat the system when that is a total lie. they can even use less storage than native packages let alone comparing it to flatpak…





Anything portable.
aisap uses bwrap it is mentioned in both links I gave you.
appman used to have firejail sandbox but it was dropped in favor of aisap because of that.