Hi All, I know it was asked multiple times but I’m a noob.
What is the best way to access my server from external network? I know I can open a port on router (not recommended), Tailscales, Wireguard or Direct VPN. I will access from android phone and maybe from other devices.
What I want to try to access (mainly docker on NAS)
- bitwarden
- calibre
- setup home assistant
- possibly RSS server
- nextcloud
- plex server (already remote access)
- maybe docker apps too
Thanks
You could use Cloudflare Tunnels. If you want to be the only one with access to them, you could set it in your private networks, which are only accessible to you on any device with the WARP client installed.
So really you have a decision to make here. Will you always have access to the VPN when you want to use those services. I suspect the answer is no in practicality. So I prefer to use something like Cloudflare tunnels to provide secure access to my network resources I’m choosing to share. I dont have to worry about ever use and every device always using a VPN. That’s just my preference though. It should be noted that I believe video and audio streaming is still against thr ToS for cloudflare tunnels. So for those applications I night use a different strategy like a VPN or wireguard.
An option is to set up WireGuard vpn as well couple it with your internal DNS for all those services, and nginx proxy manager to grab certs which you’ll need for hosting Bitwarden/vaultwarden.
443/80 get opened and pointed to nginx which has acl only allowing internal access, then whatever port you choose for WireGuard. On your phone setup the WireGuard app for on demand access once you’re not on your home wifi and job done.
I’m fairly noob-ish but have run Tailscale like this for about a year:
Tailscale on your NAS runs as the host and when you open the Tailscale app on your phone you copy the IP it gives you and use that (plus the port that your services like Bitwarden, Calibre etc each use). Eg.
100.121.9.23:8081THAT’s the sort of IP you the add to the Bitwarden app or type into your web browser.
I’m pretty amateur with tech but found Tailscale pretty easy to set up and run.
I managed to get this setup: cloudflare (not tunnel) and nginx. I hope all is well with security, certs as I have vaultwarden there (behind 2fa).
Is there a way to check security of this connection? I used Mozilla Observatory and similar. My worry is that I see traffic from other countries (analytic in cloudflare). Should I worry or this is normal scanning?
I now locked cloudflare so it is only accessible from my country.
I use tailscale for this with no issues. It traverses my CGnat without significant speed reduction. Just install tailscale on the hosts with the services on them and use magic dns or install tailscale on a vm/container and have it advertise your home subnet as a subnet router.
I know I can open a port on router (not recommended)
This is basically the only option you have if you want to provide access from external to selfhosted applications. Just forward the desired ports to the machine where the services are running on.
The less entry points you have, the better. You could “bundle” all web-based applications on port 443 and use a reverse proxy to route the traffic to the actual port based on the hostname the access was done on.
So in your router you define that all https traffic (port 443) is forwarded to your server, and on your server there is running a reverse proxy listening on port 443. All of your applications are listening on different ports that are not accessible from external. The reverse proxy then takes the hostname used for access and proxies the traffic to the actual host based on that hostname.
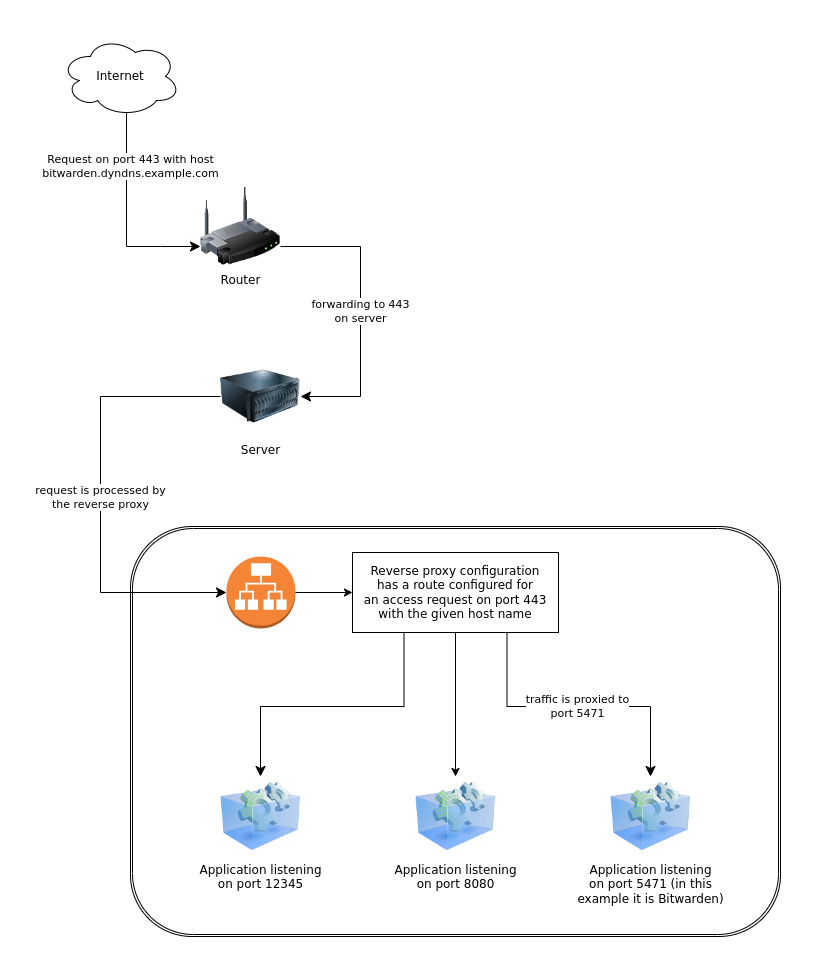
With this you have only one port open on your router and this one port is only forwarded to one single machine. Everything else is handled by that machine.





