Until yesterday, I didn’t even know you could use the docker images and the same docker-compose configs with Podman.
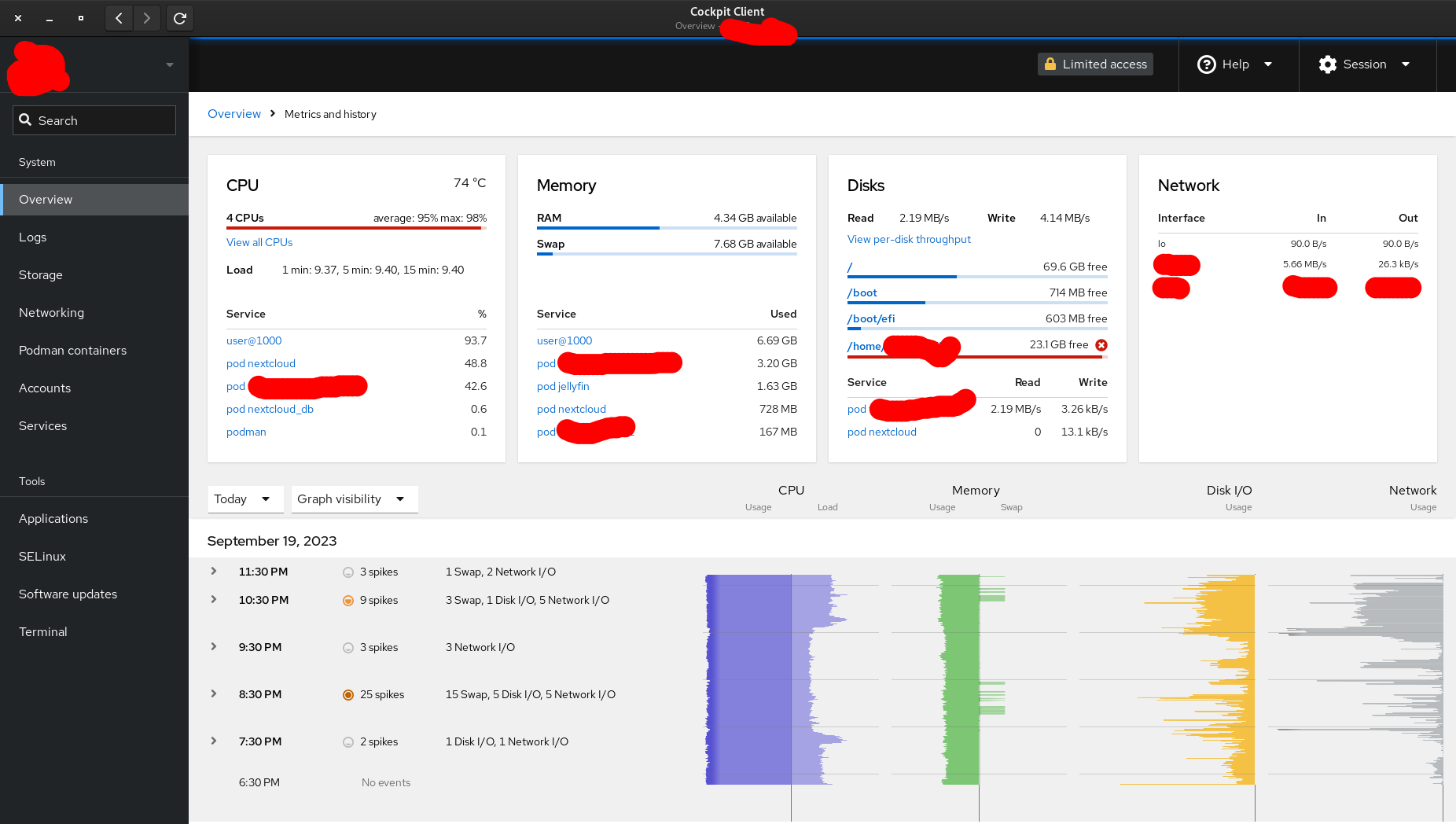
The UI you are looking at is Cockpit, which can be installed on almost any Linux Server. I have used it before but I am amazed by its integration with Podman.
Seriously, consider trying this, once.
Here’s another screenshot of Cockpit:
podman is almost AFAIK 1:1 compatible with docker, the team does great work on it
welcome to fedora!
Yes, it is! If you just run
alias docker=podman, you won’t even have to remember that you’re running Podman, and not Docker.I am still having problems with SELinux, though, so I have just turned it to permissive. Any guides for that?
An RPM exists called podman-docker, which essentially maps docker commands to podman
For SELinux, set
security_opt=label:type:container_runtime_tand make sure that volumes have the z or Z option.Isn’t that alias already present on Fedora by default?
It isn’t in my installation. I just checked.
I think the only issues I ran into were creating multi architecture manifests in podman, it doesn’t work. I had to switch to docker for that use case.
I originally excited by Podman, but ultimately migrated away from it. Friendship ended with Ubuntu and Docker -> CentOS and Podman -> Proxmox + Debian LXC (which has its own irritations but anyway). Off the top of my head:
- Can’t attach a containers to multiple networks. Most of my Docker Compose stacks have an Nginx reverse proxy and a network for each service.
- But you can use pods. However since they share the same network interface if you have multiple legacy services that both insist on, say, port 80 they can’t be in the same pod. They also don’t isolate services, nor can you assert a specific pod is the one listening on a forwarded port.
- Pods also have DNS issues with Nginx. It kept crashing since it couldn’t resolve the hostnames of the other containers in the pod, even if they were already running. If you launch a shell inside an Nginx container the other container hostnames resolve fine. I suspect the problem is the container is launched before its behind-the-scenes DNS infrastructure is ready.
- Podman lets you use secrets on normal containers (yay) but if the secret changes you have to recreate the container. Amazing synergy with rotating TLS certificates.
- Endless issues with SELinux and bind mounts. My Nginx container kept crashing because SELinux didn’t like the TLS certificate bind mount. This is where I reflected on the endless parade of random issues that I had no interest in solving and finally threw in the towel.
I brought all this up in another community and was told the problem was [paraphrased] “people keep trying to use Podman like they use Docker” - whatever that means. I do like a number of design choices in it, like including the command used to create containers in the metadata, and how it’s easy to integrate into SystemD for things like scheduled updates.
Cockpit is pretty slick though, need to install it on my bare metal Debian host.
how do you use proxmox + debian lxc?
I use that too, but run services + caddy reverse proxy with docker compose inside
I’ve read that docker should not be used inside containers, but it has worked for me. I have wireguard in a VM, I think I had some issues there
Mostly just as a wrapper for Docker. The main issue I’ve run into is Docker’s union file system functionality doesn’t work when backed by ZFS, so disk usage can balloon out of control. I wouldn’t use this in production but don’t tell me how to live my life mom.
Beyond various Docker stacks I also have a Certbot container that uses Snap (sigh), and Hashicorp Vault container which runs as a vanilla SystemD service. I run Wireguard as part of my OPNSense VM. That’s something I would run in a VM since it’s exposed to the internet. I have an older MinIO and Concourse CI Docker Compose config that I’d love to run in LXC but I suspect that isn’t realistic.
Note on Vault, I haven’t been able to get mlock to work (used to prevent sensitive memory from being swapped). By all accounts it should just work in LXC, but since it isn’t and there’s no swap on the host I just turned it off. I may migrate Vault to a VM at some point.
I’m personally just interested in lightweight environments with good enough isolation and don’t break all the time over nothing. Docker mostly accomplishes that for me. LXC + Docker also mostly accomplishes that.
(My heart yearns for FreeBSD Jails but with decent tooling)
I use Docker inside Debian LXC on Proxmox, there’s a way to avoid the crazy disk usage and it works really nicely. I followed these blog posts:
https://theorangeone.net/posts/docker-in-lxc/
https://theorangeone.net/posts/docker-lxc-storage/
I’m certainly not using it in production but it’s great in the home lab.
Tangential to the main subject here, Cockpit is awesome and everyone should be using it. You don’t have to be on a Red Hat distro either, it works beautifully on Ubuntu or Debian or whatever else you’re running. The log viewer and PCP integration (for performance metrics) are particularly standout features.
I also highly recommend the Navigator plugin from 45Drives, which adds a complete file browser and simple text file editor.
I second this statement. Cockpit is one of the best things for me when it comes to managing a Linux VM.
Welcome on board :)
I documented a bit how to run Lemmy via Podman here: https://f-hub.org/Solarpunk/lemmy-podman
Judging by the screenshots, this looks very similar to Portainer. Are they basically the same tool set for different container architectures? Looks pretty interesting.
Podman replaces the underlying container engine (the docker component). Portainer is a webUI that sits on top of Docker and provides you with tools to manage it. The Podman plugin for Cockpit just happens to do the same thing.
You can actually use Portainer with Podman if you want to. It’s a little fiddly to set up, but it works.
The main advantage of Podman is that it’s rootless by default, whereas rootless Docker is still a somewhat tricky beast to set up.
This is good info, thank you for taking the time to elucidate.
Cockpit is more of a web admin panel, and happens to have Podman integration.
I think so. But portainer may have more features.
podman-composeis not officially developed by the team that develops Podman, so it is not exactly integrated within Cockpit. But portainer has all the options, including environment variables, etc. There are guides available for installing Portainer with Podman, but I am not sure how reliable it is.Cockpit is not for Podman only. We can even create and manage VMs with a display, if we install the required tools. Cockpit is a tool to manage a headless server, like storage, updates, services, etc.
@nutbutter @noride The container section is, but the rest of it is operating on the host system more like Webmin does.
Also interested in the answer to this.
Why would you move to a red hat product?
Because some people want to play with the stuff they have to support at work?
Because the RHEL ecosystem is enormous and heavily used in the enterprise?
Because some people get free licenses?
Because not everybody shares your priorities?
Is it possible to connect docker / podman directly to the router? I’m operating an L2 bridge https://developers.redhat.com/articles/2022/04/06/introduction-linux-bridging-commands-and-features systemd-nspawn containers can connect to my router directly, but how to do it with docker / podman?
I started with podman and wanted to like it. Ultimately moved to docker because of docker compose
Compose works with podman too, you just need podman system service & to set the DOCKER_HOST env var to it’s socket.
So that’s why my containers aren’t restarting automatically on boot. Thanks!
This needs a pin
Thanks for sharing! I think I’ll implement the alias in the near future once I get more comfortable w/ Docker








